/ed724230-84fb-46c9-b239-b24e89c0c738_1.png)
Press Statement on Recent Cyberattack Outage
Review Rating Score
Today, the internet touches almost every aspect of our lives. The internet is a worldwide connected network that consists of millions of private, public, academic, business, and government networks, of local to global scope, that are linked by a broad array of electronic, wireless, and optical networking technologies. We all have become dependent on the internet and digital systems to maintain business and commerce, and more. Cyber-attacks and disruptions are hazardous threats arising from intentional or unintentional incidents that cause a breach in security, damage to digital devices and networks, or a network outage.
For this reason, more and more companies implement various security measures but what if it went wrong. How to inform your customers, suppliers, partners? This free to download press statement can be used to explain to them what happened, what the impact was, and how counterattacked the threat. The document has been created in Word using the DOCX format and therefor is fully adjustable.
Example:
[Company-name], today announced it was the victim of a cyberattack that encrypted some of our systems on [date]. As a result, many of our online services were interrupted including website functions, customer support, customer-facing applications, and company communications. We immediately began to assess the nature of the attack and started remediation. We have no indication that any customer data, including payment information was accessed, lost or stolen. Additionally….
Affected systems are being restored and we expect to return to normal operation over the next few days. We do not expect any material impact to our operations or financial results because of this outage. As our affected systems are restored, we expect some delays as the backlog of information is being processed. We are grateful for our customers’ patience and understanding during this incident and look forward to continuing to provide the exceptional customer service and support.
For more information, visit [company-name]'s virtual pressroom at [website-url], contact the Media Relations department at [tel-no], or follow us at facebook.com/[fb-account-name], twitter.com/[tw-account-name], instagram.com/[insta-account-name] or youtube.com/[yt-account-name].
Is the template content above helpful?
Thanks for letting us know!
Reviews
Earlene Golden(11/30/2020) - GBR
Template goes beyond the stars
Last modified
Our Latest Blog
- The Importance of Vehicle Inspections in Rent-to-Own Car Agreements
- Setting Up Your E-mail Marketing for Your Business: The Blueprint to Skyrocketing Engagement and Sales
- The Power of Document Templates: Enhancing Efficiency and Streamlining Workflows
- Writing a Great Resume: Tips from a Professional Resume Writer
Template Tags
- cyber security job description
- information security analyst job description cyber security analyst job description
- cyber security engineer job description
- soc analyst job description
Need help?
We are standing by to assist you. Please keep in mind we are not licensed attorneys and cannot address any legal related questions.
-
Chat
Online - Email
Send a message
You May Also Like
Important Notice: School Fees Will Increase in April – Read Our Price Increase Letter

Download Missed Appointment Letter in PDF - Prompt Notification of Missed Appointment
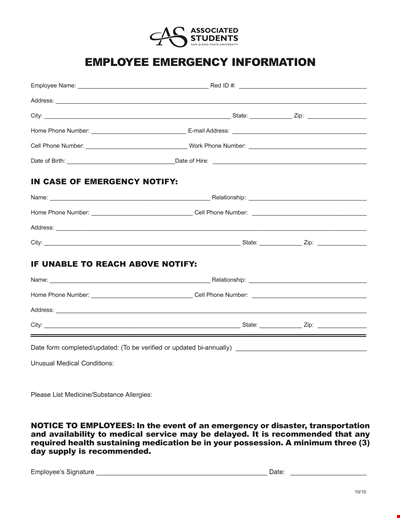
University Employee Emergency Notification Form
Get a Doctor's Note quickly at Seagold Centre in Centurion - Equestrian
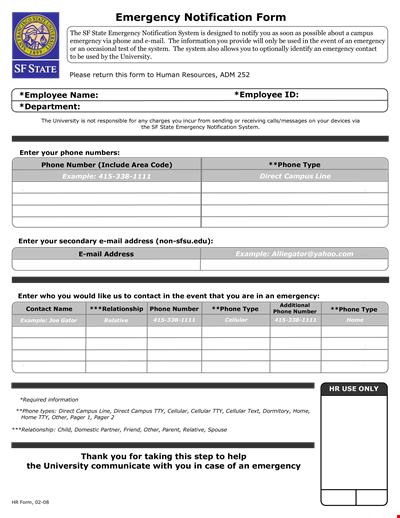
Interactive Emergency Notification Form for Employee | Phone System | Campus
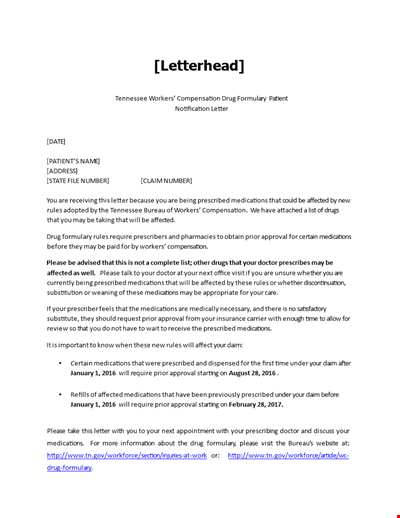
Patient Notification: Medications Affected by Recent Changes in Prescribed Treatment
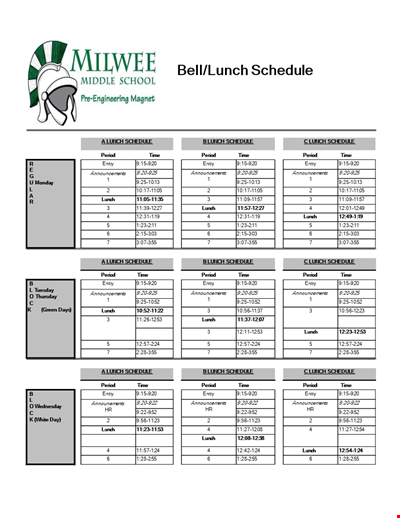
Lunch Schedule and Period Announcements: Stay updated on our lunch timings and entry procedures
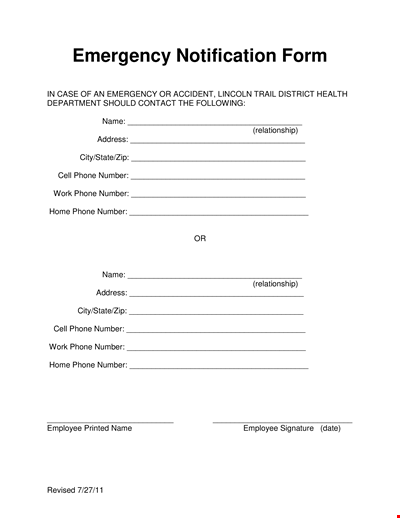
Emergency Notification Form for Health Department Employees | Phone Numbers, Relationships
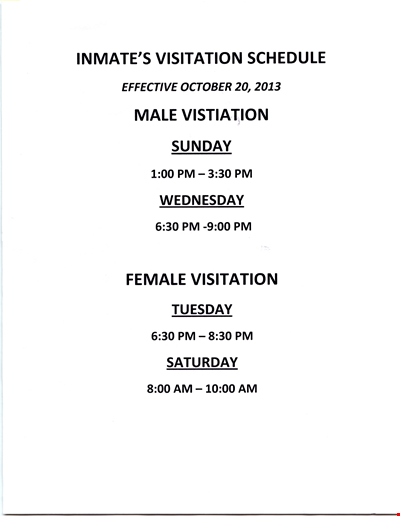
Inmate's Visitation Schedule
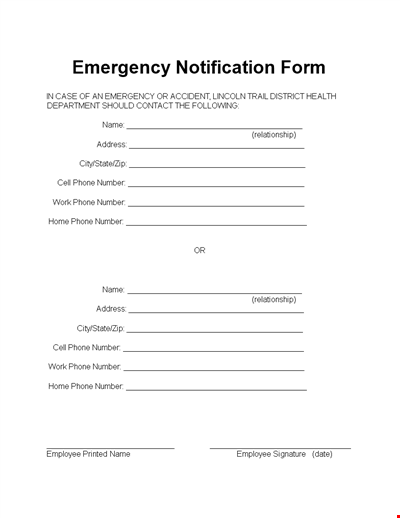
Health Department Employee Emergency Notification Form
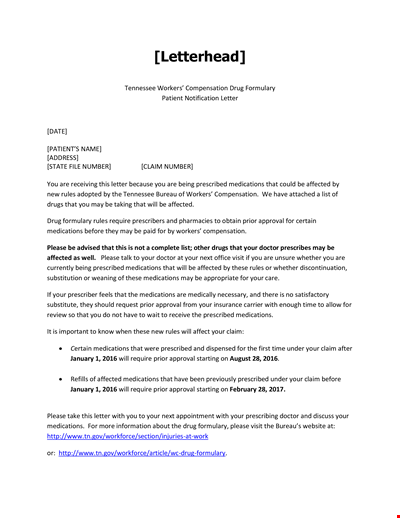
Patient Notification Example
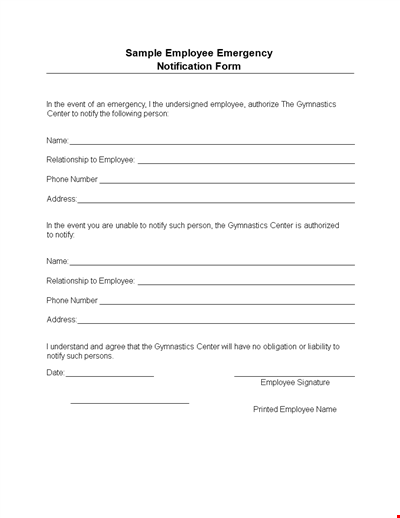
Emergency Notification Form for Gym Employees
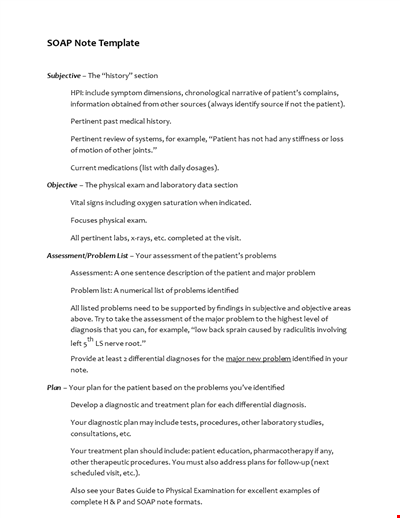
Soap Note Template
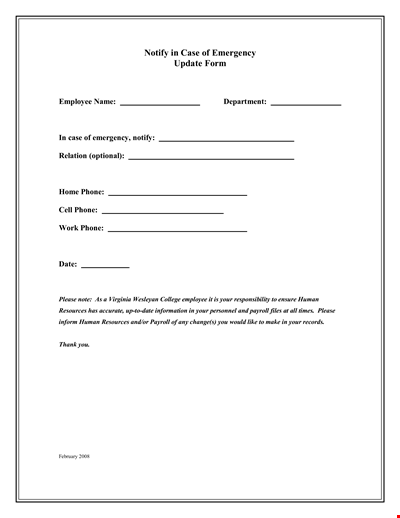
Employee Emergency Notification Update Form
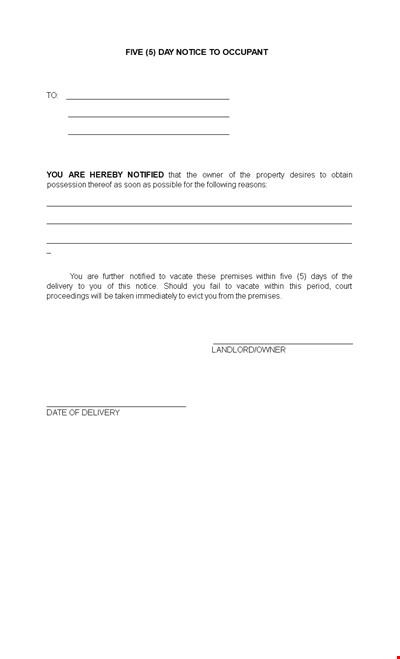
Notice to Occupant: Owner Notified - Vacate Within Five Days
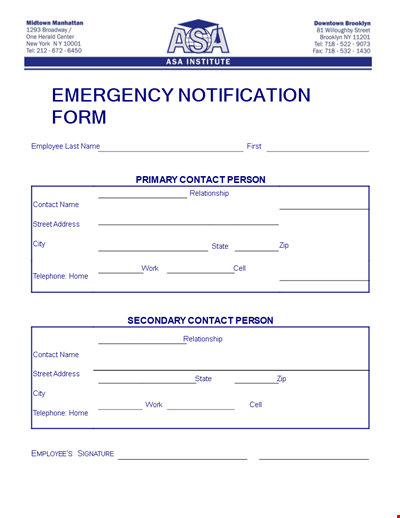
Institute Employee Emergency Notification Form