AUP Cyber Security
Review Rating Score
Realizing and adopting information security policies within your organization is an important step in ensuring that every department and employee understands their role in helping protect your company, customers, and employee data again security threats from outside and within (cyber security protection).
An Acceptable Use Policy or so-called AUP is a series of rules that define what end users may or may not do with their technology. Usually, this policy requires some kind of acknowledgment that the rules are well understood, including potential consequences of violation, before issuing any kind of log into the system. Acceptable use policies outline for example what is appropriate and what is inappropriate when it comes to using the organization’s network and the internet.
A well-defined and implement UAP policy not only outlines these rules but also explains the reason why they are implemented and important so that all the people within your organization will acknowledge them and not see the rules as arbitrary or unreasonable.
Feel free to use this editable UAP template in Word as a starting point to get your organization on the right track when it comes to full policy creation and adoption and customize it to fit your organization’s needs. This sample policy is not legal advice or a substitute for consultation with qualified legal counsel. Laws vary from country to country.
This sample includes:
- The definition and area of acceptable usage (Overview, purpose, and scope)
- Access management and authorization;
- Authentication and password protection;
- Computer Desktop policy and login/logout rules;
- Data security and protection;
- Email and messaging policies (Electronic Communication);
- Usage of social media;
- Hardware and software management;
- Internet Usage and Access policies;
- BYOD and mobile devices rules;
- Identification (Physical Security);
- Usage of removable storage/media (including USD devices);
- Security training and awareness policies for new employees;
Is the template content above helpful?
Thanks for letting us know!
Reviews
Sharita Fields(6/19/2022) - NZL
Many thanks for this.
Author. Content was provided by:
Elizabeth Davis
Elizabeth is from the sunny desert city of Phoenix, Arizona. She is thrilled to connect with professionals and like-minded individuals who share a passion for social technologies, content creation, and the exciting possibilities that AI brings to the world of social media. Her hobbies are hiking, climbing, and horse riding. Elizabeth has a master's degree in Social Technologies that she received at the ASU (Arizona State University). As a freelancer, she mostly contributes content related to IT. This includes articles on templates and forms provided by our community.
Follow Elizabeth
Last modified
Our Latest Blog
- The Importance of Vehicle Inspections in Rent-to-Own Car Agreements
- Setting Up Your E-mail Marketing for Your Business: The Blueprint to Skyrocketing Engagement and Sales
- The Power of Document Templates: Enhancing Efficiency and Streamlining Workflows
- Writing a Great Resume: Tips from a Professional Resume Writer
Template Tags
- aup computer security
- acceptable use policy information security
- acceptable use policy it security
- shopify cyber security jobs
Need help?
We are standing by to assist you. Please keep in mind we are not licensed attorneys and cannot address any legal related questions.
-
Chat
Online - Email
Send a message
You May Also Like
Event Risk Management Plan
Business Policy Template - Create Your Custom Policy
FDA Strategic Action Plan for Safety of Products
Inclement Weather Policy for Sb Policy: School Guidelines for Students and Weather
Motorcycle Policy, Safety, Service & Training - CNGO
HR Corporate Strategic Plan: Action and Engagement
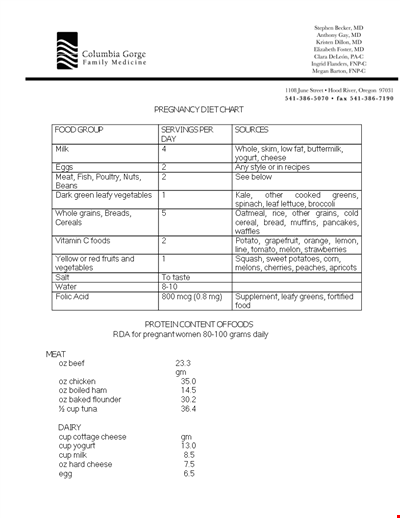
Pregnancy Diet: PDF, Medications, and Avoidance Guidelines
Effective Staff Training Agenda for Emergency Preparedness and Disaster Management

Financial Statement Controls - Streamlining Finance Workflow
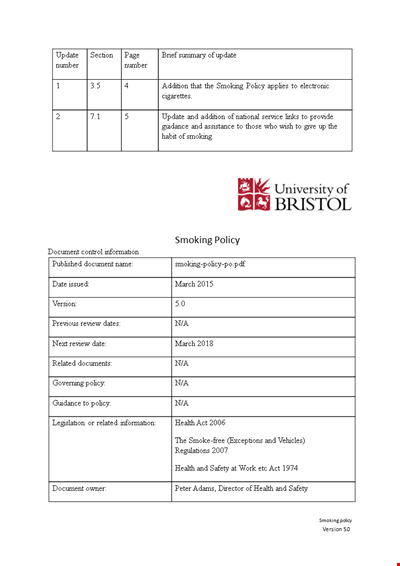
University Smoking Policy: Promoting Health and Enforcing Smoke-Free Campus
Employee Disciplinary Policy - April | Fair Hearing Process
Policy for Letter of Intent - Guidelines for Letter, Promotion, and Title for Faculty Chair
Assess Your Company's Employees and Gather Valuable Comments for Improvement
Marion Environmental Management: Your Comprehensive Environmental Policy Solution
Drug Testing Consent Agreement Form - Policy for Controlled Substance Testing at Citadel
Information Security Procedures: Ensuring Agency Safety and Compliance