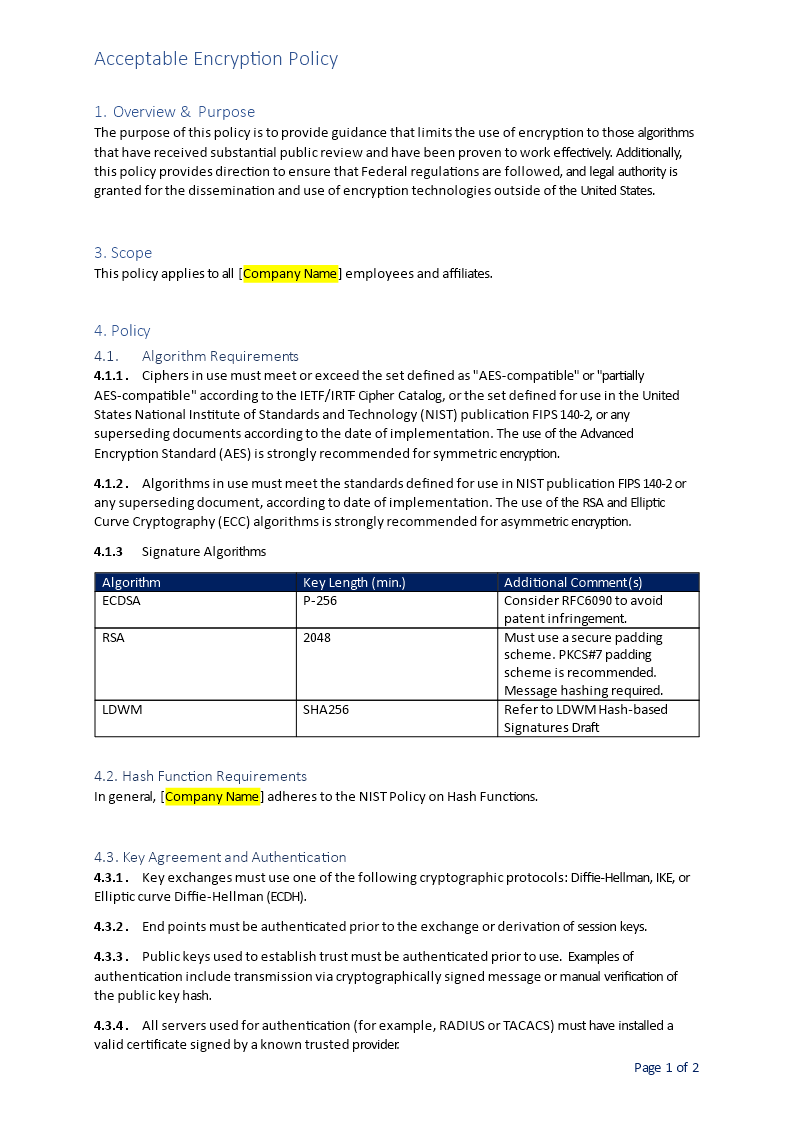
Acceptable Encryption Policy
Review Rating Score
The goal of this policy document is to provide guidance that limits the use of encryption methodologies to those algorithms that have received substantial public review, have been proven to work effectively and are secure. Additionally, this policy provides direction to ensure that regulations are followed, and legal authority is granted for the dissemination and use of encryption technologies outside of the US.
This example policy is created in Word (.DOCX) and can easily be adjusted and printed. Feel free to download the document. The document contains the following sections:
- Overview and purpose
- Scope
- Policy (including algorithm requirements, signature algorithms, and hash function requirements)
- Policy Compliance
- Related Standards, Policies, and Processes
- Revision History
Is the template content above helpful?
Thanks for letting us know!
Reviews
Jim C.(8/5/2020)
Thanks. Very useful!
Justin M.(8/5/2020)
Thanks for this great template. This was exactly the policy I was looking for to implement at our company
Author. Content was provided by:
Elizabeth Davis
Elizabeth is from the sunny desert city of Phoenix, Arizona. She is thrilled to connect with professionals and like-minded individuals who share a passion for social technologies, content creation, and the exciting possibilities that AI brings to the world of social media. Her hobbies are hiking, climbing, and horse riding. Elizabeth has a master's degree in Social Technologies that she received at the ASU (Arizona State University). As a freelancer, she mostly contributes content related to IT. This includes articles on templates and forms provided by our community.
Follow Elizabeth
Last modified
Our Latest Blog
- The Importance of Vehicle Inspections in Rent-to-Own Car Agreements
- Setting Up Your E-mail Marketing for Your Business: The Blueprint to Skyrocketing Engagement and Sales
- The Power of Document Templates: Enhancing Efficiency and Streamlining Workflows
- Writing a Great Resume: Tips from a Professional Resume Writer
Template Tags
Need help?
We are standing by to assist you. Please keep in mind we are not licensed attorneys and cannot address any legal related questions.
-
Chat
Online - Email
Send a message
You May Also Like
Sample Leadership Retreat
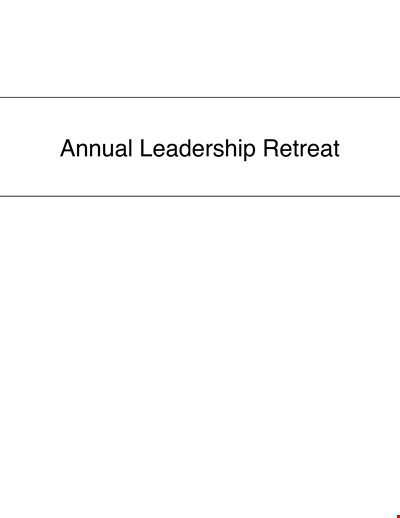
Seedling Price List - Affordable Saplings for Your Garden | Buy Best Quality Seedlings Online
Colored College Ruled Paper
College Ruled A Size Paper Template
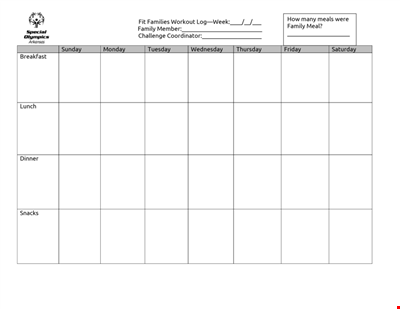
Get Fit as a Family with our Printable Workout Log | Track your progress and stay motivated
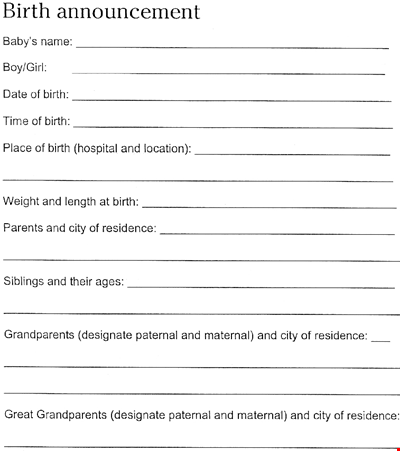
Download Beautiful Birth Announcement Template
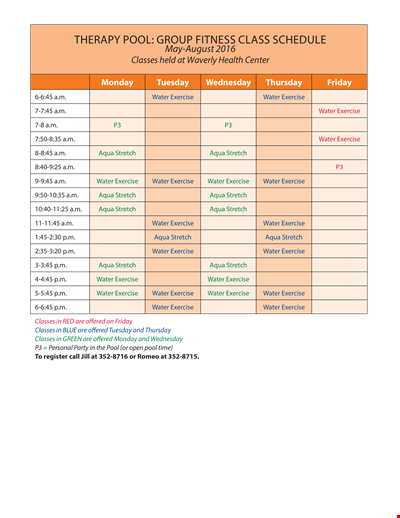
Fitness Therapy Schedule Template - Water, Exercise Classes, Stretch
Excellence in Education
Download MLA Reference Style Format: The Ultimate Guide with Examples
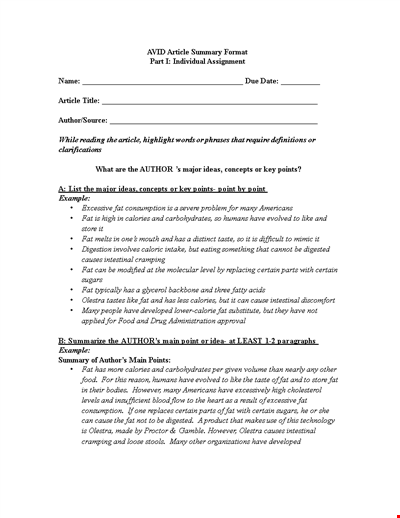
Sample Article Summary Template - Write Effective Summaries Easily
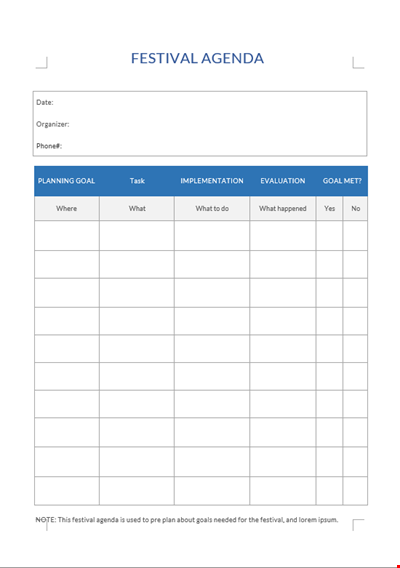
Festival Agenda A4

Fact Sheet Template - Health, Water, Copper, Drinking Levels

Social Event Program Layout
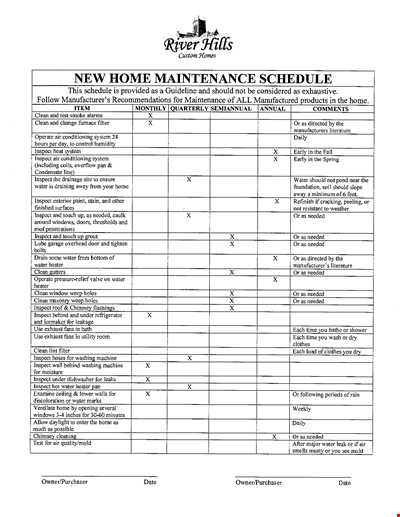
Organize Your Home Maintenance with our New Template
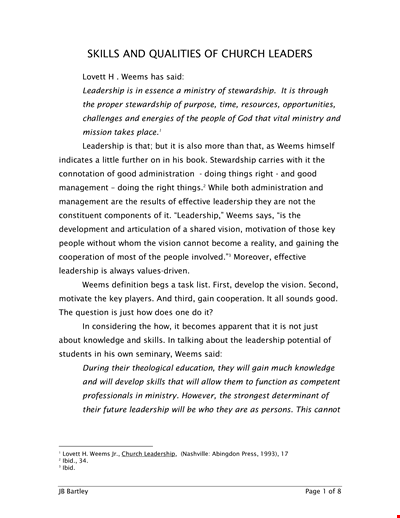
Church Leadership Qualities Example
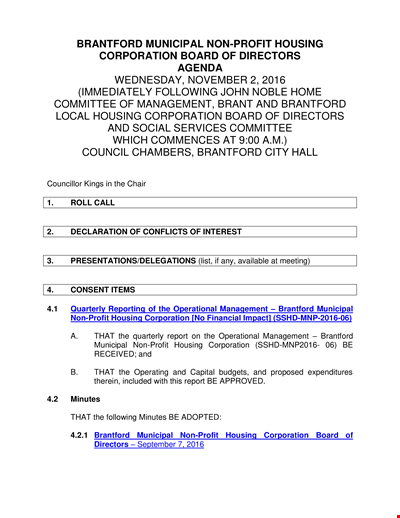
Non Profit Board Agenda