/e904630a-bbf8-459b-b5f2-4da99ac8c0d3_1.png)
Chief Information Security Officer Job Description
Review Rating Score
An effective CIO job description is vital when attracting the right talents. Use this Chief Information Security Officer Job Description template for your inspiration when you need to create a job posting that is clear and concise.
What is a good job description for an Chief Information Security Officer?
For this position, we are looking for a fully accessible individual who can handle difficult situations while also adhering to our organization's laws and regulations. He must be disciplined in all aspects of his work. These selected candidates must be selected and posted on different branches of the company for providing their services.
This sample Job description explainer offers guidance on key sections that are important to include for clarity, as well as suggestions for promoting the position. It provides a list of duties, responsibilities, tasks, requirements, demands for setting job expectations and the employee's ability to perform the work as described. However, it’s often not construed as an exhaustive list of all functions, responsibilities, skills and abilities.
What does a Chief Information Security Officer do?
Responsibilities:
- Facilitate risk assessment and risk management procedures by working directly with business units.
- Develop and improve a framework for managing information security.
- To ensure the uniform implementation of policies and standards across all main projects, platforms, or services, comprehend and engage with related disciplines through committees.
- Assume command of the company's information security organization.
- Collaborate with business stakeholders across the organization to enhance risk management awareness.
- Assist with overall corporate tech strategy by bringing current expertise and a vision for the future of systems and technologies.
Qualifications:
- A Bachelor of Science in business administration or a similar subject is necessary.
- Certification in security management for professionals
- A minimum of eight to twelve years of combined risk management, information security, and IT expertise is required.
- Outstanding written and spoken language skills, as well as a high importance of interpersonal ethics
- Proficiency with contractual and supplier discussions and supervision, including managed services, Innovative thinking and leadership with the ability to lead and encourage cross-functional, interdisciplinary teams
- Experience with Agility (scaled) computer programming or other best growth approaches is preferred.
Is the content above helpfull?
Thanks for letting us know!
Reviews
Kayleigh Beltran(12/24/2021) - NZL
Very good!!
Bertha Vega(12/24/2021) - DEU
Have a drink on me
Last modified
Our Latest Blog
- The Importance of Vehicle Inspections in Rent-to-Own Car Agreements
- Setting Up Your E-mail Marketing for Your Business: The Blueprint to Skyrocketing Engagement and Sales
- The Power of Document Templates: Enhancing Efficiency and Streamlining Workflows
- Writing a Great Resume: Tips from a Professional Resume Writer
Template Tags
Need help?
We are standing by to assist you. Please keep in mind we are not licensed attorneys and cannot address any legal related questions.
-
Chat
Online - Email
Send a message
You May Also Like
Product Manager Real Estate Job Description
Restaurant Waiter Job Description | Manager | Customer Service | Serving Customers
Resort Nanny Job Description | Caring for Children, Cleaning, Assisting Parents

School Treasurer Job: Activities & Responsibilities

Pod Nanny Job Description: Experienced Nannies for Your Child's Education and Care
Administrative Job Description Template for Manager | Department | Agency | Administrative
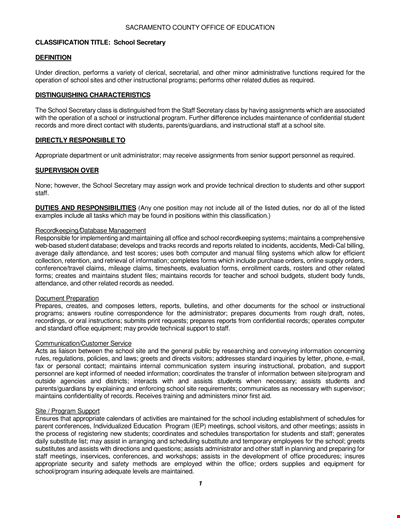
School Secretary Job Description: Office Staff & Personnel for Students
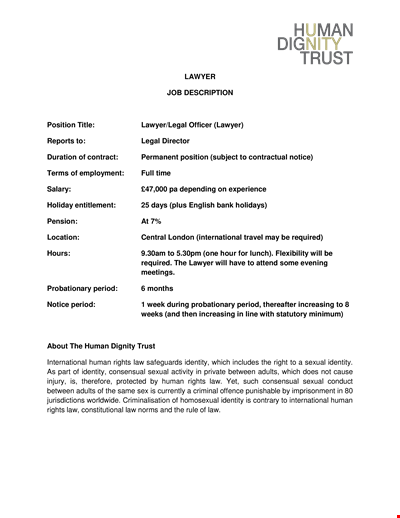
Legal Lawyer Job Description | Find Your Legal Career Here
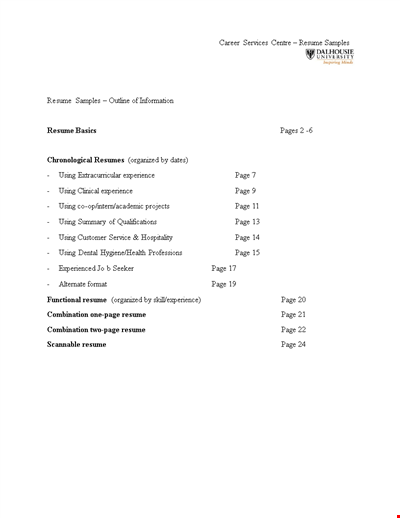
Free Download: HR First Job Resume Template | University, Experience, Skills, Relevant | Halifax
![Foundation Treasurer Job Description [Financial]](/Storage/Media/109904ba-dc0e-4f88-9dc6-706f7f6f6033.png?w=400&h520&format=png)
Foundation Treasurer Job Description [Financial]
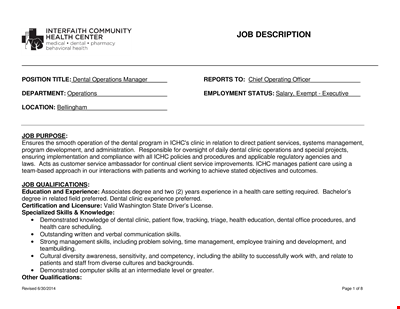
Dentist Operation Manager Job Description - Dental Program and Appropriate
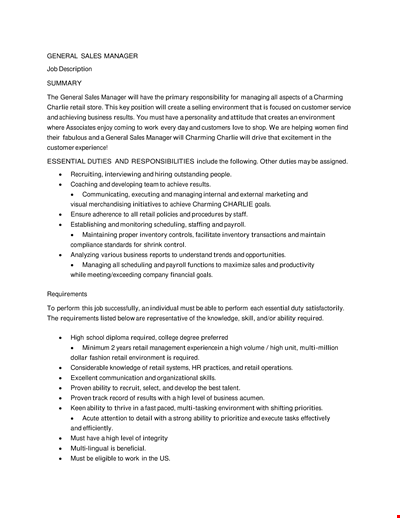
Download Free General Sales Manager Job Description Template for Retail | Charlie - Charming
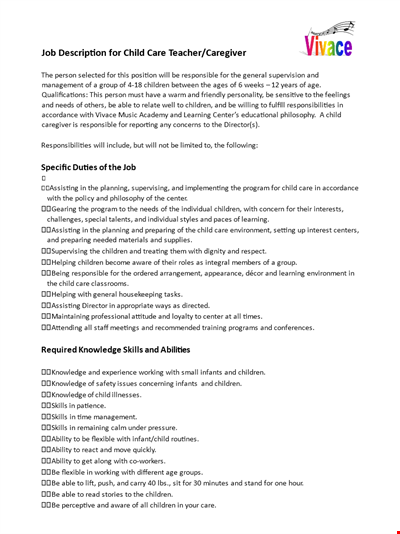
Child Caregiver Job Description and Responsibilities for Caring for Children with Knowledge
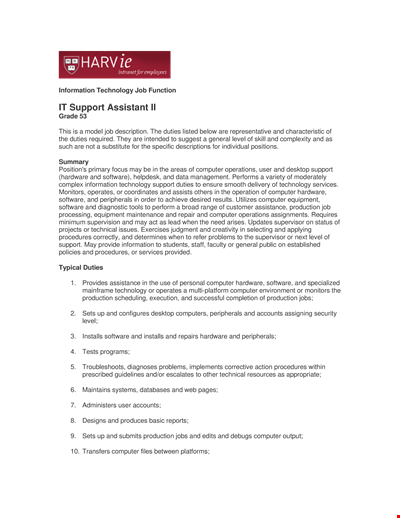
IT Support Job Description: Software, Hardware, and Production Duties for Computer-related Support
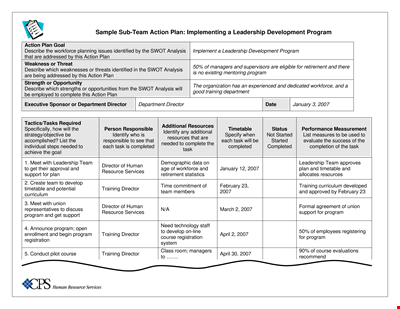
Sub Team Leader Action Plan Template
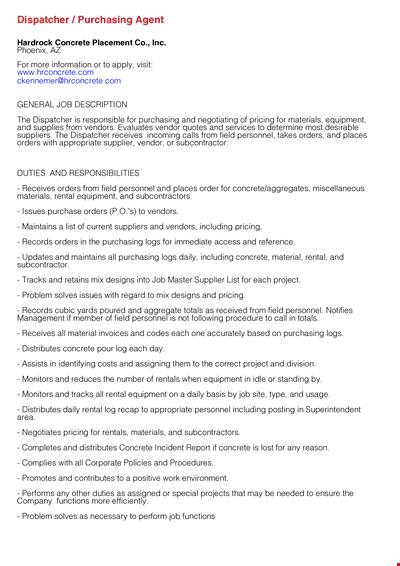
Dispatcher Purchasing Agent Job Description